News
Who Are the Inventors of Electricity Explained Clearly

Electricity powers nearly every aspect of modern life, from smartphones and hospitals to transportation and global communication. Yet one of the most common questions people ask is who are the inventors of electricity and how this life-changing force actually came into existence. The answer is more complex than a single name, because electricity was not invented overnight. Instead, it was discovered, studied, refined, and applied by many thinkers over thousands of years.
This article provides a clear, authoritative, and easy-to-understand explanation of how electricity developed, who played the most important roles, and why their work still matters today. By the end, you will not only understand the historical truth behind the question but also gain insight into the benefits, challenges, and real-world impact of electrical innovation.
Understanding the Question: What Does “Inventing Electricity” Mean?
Before identifying who are the inventors of electricity, it is important to define what “invention” means in this context. Electricity is a natural phenomenon, not a man-made object. Humans did not create electricity; they discovered it, learned how it behaves, and eventually figured out how to generate, control, and distribute it.
In simple terms, electricity was not invented by one person. It was developed through centuries of observation, experimentation, and engineering. Some contributors identified electrical effects, others explained the science, and later inventors transformed theory into practical systems that power the modern world.
Early Discoveries That Laid the Foundation
Ancient Observations of Electrical Phenomena
The earliest known observations of electrical effects date back to around 600 BCE. Thales of Miletus, an ancient Greek philosopher, noticed that rubbing amber with fur caused it to attract small objects. While he did not understand electrons or charge, this observation marked humanity’s first recorded encounter with static electricity.
Although Thales is not usually listed as a direct answer to who are the inventors of electricity, his work is critical because it represents the starting point of electrical curiosity.
Key Scientists Who Shaped Electrical Science
William Gilbert and the Birth of Electrical Science
In the late 16th century, English scientist William Gilbert conducted systematic experiments on magnetism and static electricity. He coined the term “electricus,” derived from the Greek word for amber. Gilbert’s work transformed scattered observations into a scientific discipline, making him one of the earliest true pioneers of electrical science.
Benjamin Franklin and the Nature of Electricity
Benjamin Franklin is one of the most widely recognized figures when discussing who are the inventors of electricity. His famous kite experiment in 1752 demonstrated that lightning is a form of electrical energy. Franklin introduced key concepts such as positive and negative charge and contributed practical inventions like the lightning rod.
Franklin’s work bridged the gap between theory and real-world safety, showing that electricity could be understood and controlled.
The Inventors Who Made Electricity Usable
Alessandro Volta and the First Battery
In 1800, Italian scientist Alessandro Volta created the first electric battery, known as the voltaic pile. This invention allowed scientists to produce a steady flow of electric current for the first time. Volta’s breakthrough made controlled experimentation possible and laid the groundwork for modern electrical engineering.
When people ask who are the inventors of electricity in practical terms, Volta is often included because he enabled electricity to be generated on demand.
Michael Faraday and Electromagnetic Induction
Michael Faraday’s discoveries in the 19th century changed the world forever. He demonstrated electromagnetic induction, the principle behind electric generators and transformers. Faraday showed that mechanical motion could be converted into electrical energy, making large-scale power generation possible.
Modern power plants, regardless of energy source, rely on Faraday’s principles.
Edison, Tesla, and the Power Wars
Thomas Edison and Electrical Distribution
Thomas Edison played a major role in making electricity accessible to the public. He developed practical incandescent lighting and built one of the first electrical distribution systems. Edison’s direct current (DC) system powered early homes and businesses, proving that electricity could be commercially viable.
While Edison did not discover electricity, his contribution answers part of who are the inventors of electricity in everyday life.
Nikola Tesla and Alternating Current
Nikola Tesla revolutionized electricity with alternating current (AC) systems, which could transmit power efficiently over long distances. His inventions, including AC motors and transformers, form the backbone of today’s electrical grids.
Tesla’s work resolved many limitations of DC power and enabled global electrification. Among historians and engineers, Tesla is often regarded as one of the most influential figures in electrical history.
A Clear Answer: Who Are the Inventors of Electricity?
So, who are the inventors of electricity? The most accurate answer is that electricity has multiple inventors, each responsible for a different stage of discovery and application. Key contributors include Thales of Miletus, William Gilbert, Benjamin Franklin, Alessandro Volta, Michael Faraday, Thomas Edison, and Nikola Tesla. Together, their work transformed a mysterious natural force into a foundation of modern civilization.
Benefits of Understanding the History of Electricity
Understanding who are the inventors of electricity provides more than historical knowledge. It helps people appreciate how innovation evolves over time and why collaboration across generations matters.
One major benefit is educational clarity. Students and professionals gain a more accurate view of science as a process rather than a single moment of genius. Another benefit is inspiration. Many inventors faced skepticism, failure, and limited resources, yet persisted. Finally, this knowledge supports technological literacy, helping societies make informed decisions about energy, sustainability, and innovation.
Challenges Faced by Early Electrical Pioneers
The path to modern electricity was filled with challenges. Early scientists lacked precise instruments and mathematical models. Many experiments were dangerous, involving high voltages without safety standards. Financial and political obstacles also slowed progress, as competing systems and commercial interests often clashed.
Even today, misconceptions persist. One of the biggest challenges is the oversimplification of history, where people expect a single answer to who are the inventors of electricity, ignoring the collective nature of scientific advancement.
Real-World Examples of Electrical Innovation in Action
The influence of early electrical pioneers is visible everywhere. Power grids rely on Faraday’s induction and Tesla’s AC systems. Batteries used in smartphones trace their origins to Volta’s experiments. Lightning protection systems still use principles introduced by Franklin.
Hospitals, data centers, transportation networks, and renewable energy systems all represent real-world examples of how foundational electrical discoveries continue to shape daily life.
How Electricity Development Progressed Step by Step
The development of electricity followed a logical progression over centuries. First, natural electrical effects were observed and recorded. Next, scientists conducted controlled experiments to understand electrical behavior. Then, inventors developed devices to generate steady current. After that, engineers created systems to distribute electricity safely and efficiently. Finally, large-scale infrastructure transformed electricity into a universal utility.
This step-by-step evolution explains why no single person can fully answer who are the inventors of electricity.
Frequently Asked Questions About Electricity Inventors
Who officially invented electricity?
There is no official inventor of electricity. Electricity is a natural phenomenon discovered and developed by many scientists over time.
Why is Benjamin Franklin associated with electricity?
Franklin proved that lightning is electrical and introduced foundational concepts like positive and negative charge, making electricity easier to understand.
Was Nikola Tesla more important than Edison?
Both were important in different ways. Edison focused on practical applications and business systems, while Tesla developed technologies that made global power distribution possible.
Is electricity still being “invented” today?
While electricity itself is understood, new technologies for generating, storing, and using electrical energy continue to evolve, especially in renewable energy and smart grids.
Final Thoughts
Asking who are the inventors of electricity opens the door to a fascinating story of human curiosity, persistence, and collaboration. Electricity was not invented by one person but shaped by many brilliant minds across centuries. Their combined efforts transformed an invisible natural force into one of the most important foundations of modern life.
By understanding this shared legacy, we gain not only historical insight but also a deeper appreciation for the power systems we rely on every single day.

News
What Is 185.63.253.300 IP Address and Why It Appears
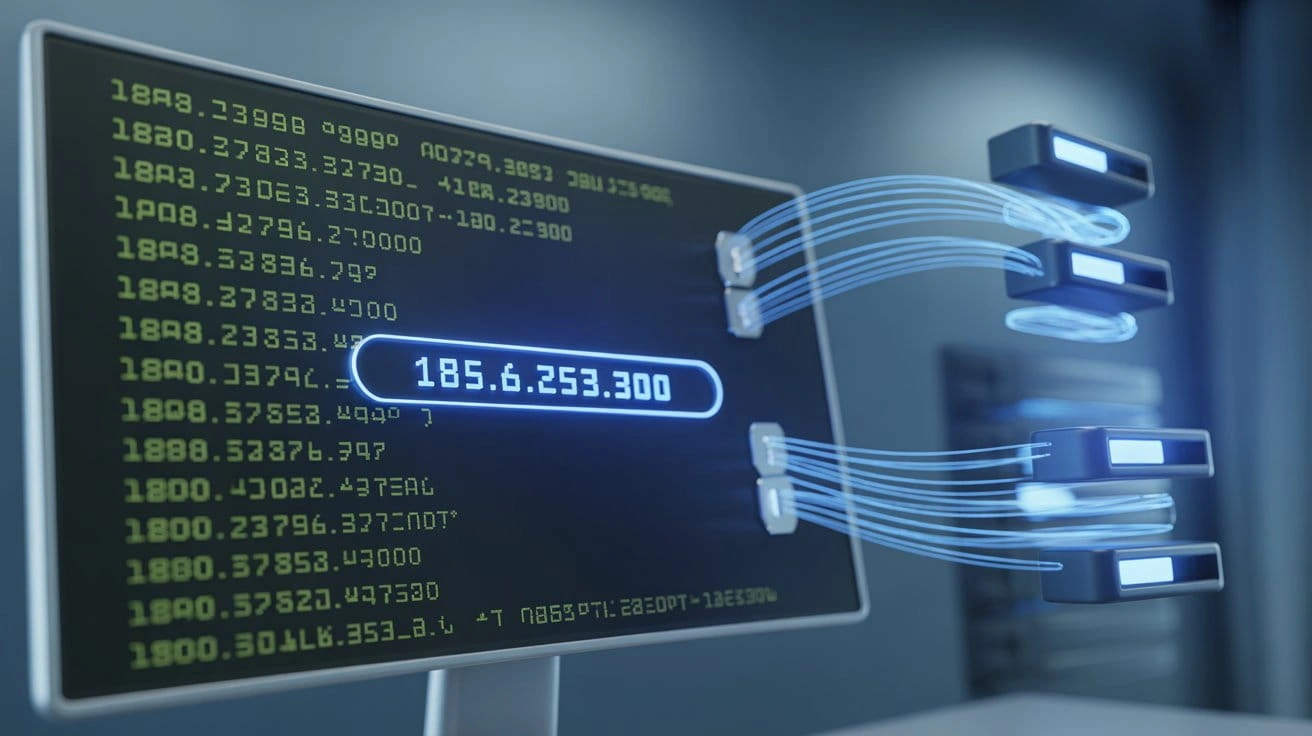
IP addresses are the backbone of internet communication. Sometimes, unusual addresses like 185.63.253.300 appear in server logs, firewall reports, or analytics dashboards. Website owners, developers, and cybersecurity professionals often want to know whether such addresses are legitimate, suspicious, or simply formatting errors.
This guide explains the meaning of 185.63.253.300, why it appears online, the risks it may pose, and the steps to analyze it effectively.
Understanding IP Addresses and IPv4 Standards
An IP address is a unique identifier that allows devices and servers to communicate on a network. IPv4 addresses consist of four numbers between 0 and 255, separated by dots.
185.63.253.300 violates this rule because the last segment exceeds 255, making it an invalid IPv4 address. This invalid format often causes it to show up in discussions, logs, or troubleshooting guides.
Why 185.63.253.300 Appears in Logs
Even though the address is invalid, it can still appear in logs for several reasons:
- Logging errors or misconfigured scripts
- Malformed data from bots or scraping tools
- Database corruption or parsing mistakes
- IP conversion issues between IPv6 and IPv4
Recognizing these causes prevents unnecessary concern and helps focus on genuine network anomalies.
Security Risks Associated With Unusual IPs
While 185.63.253.300 itself is not a valid IP, its appearance may indicate potential risks:
- Automated bots attempting to probe your servers
- Malformed traffic from misconfigured clients
- Possible data integrity issues in logging systems
Security teams analyze logs carefully to distinguish between harmless errors and suspicious activity.
Benefits of Investigating Malformed IP Addresses
Investigating addresses like 185.63.253.300 can:
- Detect misconfigurations in analytics and logging systems
- Identify automated or bot traffic
- Improve firewall rules and server monitoring
- Ensure clean and accurate network data
Challenges in Handling Invalid IP Entries
Common challenges include:
- Misinterpretation: The entry may be a logging error, not real traffic.
- Analytics inaccuracies: Malformed IPs may distort reports.
- Upstream alterations: Proxies or monitoring tools can change the original data.
Careful cross-referencing and log analysis are essential to overcome these challenges.
How to Investigate 185.63.253.300
Step-by-Step IP Analysis
- Verify logs – Check raw logs to confirm the entry.
- Analyze patterns – Look for repeated requests or unusual intervals.
- Use IP lookup tools – Compare related IP ranges.
- Check parsing scripts – Ensure no code converts valid IPs incorrectly.
- Update firewall rules – Filter out malformed traffic if necessary.
Real-World Example
A website reported traffic spikes with 185.63.253.300 appearing in analytics. Investigation revealed a script misconverted IPv6 addresses into malformed IPv4 entries. Once corrected, logs and analytics returned to normal.
Tools for IP Address Analysis
Professionals use:
- Network monitoring dashboards
- Firewall and intrusion detection systems
- Log analysis platforms
- IP intelligence services
These tools help identify unusual traffic patterns and verify whether entries like 185.63.253.300 are legitimate.
Best Practices for Managing IP Data
- Validate IP formats before storing in databases
- Monitor logs regularly for anomalies
- Correct misconfigured scripts that generate malformed entries
- Implement firewall rules to filter unusual traffic
Frequently Asked Questions
Q1: What is 185.63.253.300?
It resembles an IPv4 address but is invalid because the last segment exceeds 255.
Q2: Why does this IP appear in logs?
Mostly due to logging errors, malformed traffic, or parsing mistakes.
Q3: Is it a threat to my website?
Not inherently. It usually indicates a logging or script issue, though it could occasionally relate to automated bot activity.
Q4: How can I handle it?
Check raw logs, validate IPs, and fix scripts that produce malformed addresses.
Q5: Should I block it?
Blocking is generally unnecessary since it’s not a valid IP. Focus on root cause investigation instead.
Conclusion
The appearance of 185.63.253.300 often raises concern, but understanding IP standards shows it is not a valid IPv4 address. Most cases point to logging errors, parsing mistakes, or bot-generated malformed traffic.
By systematically analyzing logs, validating data, and using professional monitoring tools, administrators can prevent these anomalies from affecting network performance or analytics accuracy.
News
Mypasokey: A Complete Guide to Secure Digital Access

Managing digital accounts has become a daily challenge. Most people now use dozens of platforms including email, online banking, cloud tools, social networks, and streaming services. Each account requires login credentials, and remembering strong passwords for every platform can be difficult.
Because of this problem, many users are searching for mypasokey, a modern solution designed to simplify digital authentication while improving security. Instead of remembering multiple passwords, users can store and manage their credentials through one secure system.
The idea behind mypasokey is simple: reduce password overload while protecting sensitive data. It helps users access accounts faster, create stronger passwords, and avoid security risks caused by weak or repeated credentials.
This article explains what mypasokey is, how it works, the benefits it offers, possible challenges, and real-world examples of how it is used.
What Is Mypasokey
Mypasokey is a digital authentication and credential management system designed to store, organize, and protect login information for online services.
Instead of memorizing multiple passwords, users create one master credential that unlocks a secure vault containing all their stored login details. This vault is protected with strong encryption, which prevents unauthorized access.
Many modern authentication platforms like mypasokey also support password-less login methods. These methods can include biometric verification, device authentication, or encrypted keys that confirm the user’s identity.
In simple terms, mypasokey works like a secure digital key that manages access to your online accounts while keeping your information protected.
How Mypasokey Works
To understand the value of mypasokey, it helps to look at the basic process behind how it manages authentication and security.
Step-by-Step Process
- Account Setup
The user installs the application or registers on the platform and creates a master password. - Secure Vault Creation
The system creates an encrypted vault where login credentials and other sensitive information are stored. - Password Generation
The platform can automatically generate strong passwords for new accounts. - Login Assistance
When the user visits a website or application, the system can automatically fill the stored credentials. - Device Synchronization
Information can be securely synced across devices such as smartphones, tablets, and computers.
Through this process, mypasokey helps users access accounts easily while maintaining a high level of protection.
Key Features of Mypasokey
Modern authentication platforms offer a variety of features designed to improve both convenience and security. Mypasokey typically includes several important capabilities.
Encrypted Credential Storage
All login details are stored in a protected digital vault using strong encryption. This prevents hackers from accessing sensitive data.
Strong Password Generation
The system can generate unique and complex passwords that are difficult to guess or crack.
Automatic Login Assistance
Instead of manually typing usernames and passwords, the platform automatically fills the login fields for approved websites.
Multi-Device Access
Users can access their credentials across multiple devices without needing to manually transfer passwords.
Security Alerts
Some platforms monitor potential data leaks and notify users if their credentials appear in known security breaches.
These features make mypasokey a useful tool for protecting online accounts and improving the login experience.
Benefits of Using Mypasokey
Using mypasokey offers several advantages for individuals and organizations that want better control over their digital credentials.
Improved Account Protection
Weak passwords are one of the most common causes of online security incidents. With mypasokey, users can create strong and unique passwords for every account without needing to remember them.
Less Password Stress
People often forget passwords or reuse the same one across multiple websites. A centralized credential system removes this burden and simplifies access.
Faster Login Process
Automatic login assistance saves time by eliminating the need to manually type credentials.
Reduced Risk of Phishing
Because login details are only filled on verified websites, users are less likely to enter passwords on fake pages.
Organized Digital Information
Users can store various types of sensitive information, including account details, secure notes, and personal credentials.
These advantages make mypasokey an effective solution for managing digital identities.
Challenges and Limitations
Although mypasokey offers many advantages, users should also understand a few potential challenges.
Responsibility for the Master Password
The master credential protects the entire vault. If a user forgets it and recovery options are not available, access to stored data may become difficult.
Centralized Credential Storage
All passwords are stored in one system. While encryption protects the data, users must trust the platform’s security.
Learning Curve
New users may need some time to understand how the system works, especially during the initial setup process.
Advanced Features May Require Payment
Some platforms provide basic features for free, while advanced capabilities such as secure sharing or monitoring tools may require a paid plan.
Understanding these limitations helps users adopt mypasokey responsibly and effectively.
Real-World Examples and Use Cases
Mypasokey can be used in many different situations where secure access is important.
Personal Account Management
Individuals often use the platform to manage login details for services such as:
- Email platforms
- Online banking accounts
- Social media profiles
- Shopping websites
- Streaming services
Instead of repeating the same password, the system generates unique credentials for each platform.
Team and Business Collaboration
Companies frequently need to share account access among team members. Using mypasokey, businesses can share credentials securely without exposing passwords through messages or email.
Examples include:
- Managing company social media accounts
- Accessing shared software tools
- Logging into cloud services
Enterprise Identity Systems
Large organizations often use advanced authentication platforms similar to mypasokey to manage employee access to internal systems.
These systems can allow workers to log in using biometric authentication or secure device verification instead of traditional passwords.
High-Security Industries
Industries such as finance and healthcare handle highly sensitive information. Secure credential management systems help protect this data and reduce the risk of unauthorized access.
Best Practices for Using Mypasokey Safely
Even the most secure system requires responsible use. Following these guidelines can help users get the most protection from mypasokey.
Enable Additional Verification
Adding a second verification method increases protection and prevents unauthorized access.
Create a Strong Master Credential
The master password should be long, unique, and difficult to guess.
Review Stored Passwords Periodically
Updating weak passwords helps maintain strong account protection.
Keep Devices Secure
Because authentication may rely on your device, using screen locks and device security features is important.
Install Updates Regularly
Updates often include security improvements that help protect user data.
By following these practices, users can maintain a high level of digital security while using mypasokey.
The Future of Mypasokey and Digital Authentication
Digital security systems continue to evolve as cyber threats become more sophisticated. Platforms like mypasokey represent a shift toward safer and more convenient authentication methods.
Several developments are shaping the future of credential management:
- Password-less login technologies
- Biometric authentication systems
- Artificial intelligence for detecting suspicious activity
- Advanced encryption techniques
- Decentralized identity systems
As the number of online accounts continues to increase, solutions that simplify authentication while protecting user data will become even more important.
Tools like mypasokey are helping move the internet toward a safer and more efficient way of managing digital identities.
Frequently Asked Questions
What is mypasokey used for?
Mypasokey is used to securely store login credentials and help users access online accounts safely and efficiently.
Is mypasokey safe to use?
Yes. The system typically uses strong encryption and authentication methods to protect stored credentials.
Can beginners use mypasokey easily?
Most platforms are designed with simple interfaces that guide users through setup and daily use.
Does mypasokey work across multiple devices?
Yes. Many systems allow secure synchronization so users can access their credentials on phones, tablets, and computers.
Is mypasokey free?
Some services provide free versions with basic features, while advanced features may require a paid subscription.
Conclusion
Managing online credentials has become more complicated as people rely on an increasing number of digital services. Weak or repeated passwords can lead to serious security risks.
Mypasokey provides a practical solution by combining credential storage, encryption, and automated authentication in one secure system. It allows users to protect their accounts, simplify the login process, and reduce the stress of remembering multiple passwords.
As digital activity continues to grow, systems like mypasokey will play an important role in helping individuals and organizations maintain secure and convenient access to the online world.
News
Herbciepscam: What It Is and Why People Are Concerned

If you’ve searched for herbciepscam, you’re likely trying to determine whether it’s a legitimate product, a real company, or a potential fraud. Online discussions show growing curiosity and concern around this term, especially among people interested in herbal supplements and natural health remedies.
The reality is that herbciepscam is not a recognized medical brand or verified wellness company. Instead, it has become associated with questionable online practices tied to herbal product promotions. Many users search the term after encountering suspicious websites, unexpected charges, or exaggerated health claims.
This in-depth guide explains what herbciepscam refers to, why it’s trending, how similar scams operate, and what you can do to protect yourself. The goal is to provide clear, practical information that helps you make safe decisions online.
What Is Herbciepscam?
In simple terms, herbciepscam refers to alleged fraudulent online activities connected to herbal or “natural” health products. It is not a registered pharmaceutical brand, certified supplement line, or authorized medical provider.
Instead, the term is often used by consumers who suspect they’ve encountered a scam involving herbal remedies. These schemes typically rely on professional-looking websites, persuasive marketing copy, and bold promises of rapid health improvements.
Common themes include:
- Miracle weight loss
- Instant pain relief
- Detoxification cures
- Hormonal balance solutions
- Anti-aging breakthroughs
While legitimate herbal products do exist, herbciepscam is associated with offers that lack scientific backing, regulatory transparency, or verifiable company information.
Understanding this distinction is critical. Not all herbal supplements are scams, but operations linked to herbciepscam patterns tend to raise serious red flags.
The Rise of Herbciepscam in Online Searches
The popularity of natural wellness products has grown significantly in recent years. Consumers are increasingly drawn to plant-based remedies and alternative treatments. This surge in demand has created opportunities for both reputable companies and deceptive operators.
Scams like herbciepscam thrive in environments where:
- Consumers want quick health fixes.
- Regulations for supplements are less strict than pharmaceuticals.
- Social media advertising spreads rapidly.
- People trust testimonials without verification.
Fraudsters understand emotional triggers. They craft persuasive messages that appeal to pain points such as chronic illness, weight concerns, aging fears, and low energy. When consumers are desperate for solutions, they may act quickly without fully researching the source.
That urgency is exactly what these scams rely on.
How Herbciepscam Schemes Typically Work
Although each operation may vary slightly, most herbciepscam-style schemes follow a predictable structure.
Step 1: Attention-Grabbing Advertisement
The process often begins with a social media ad, pop-up banner, or search engine promotion. The ad may claim dramatic results backed by “clinical studies” or “doctor approval.”
The language is usually emotional and urgent.
Step 2: Professional-Looking Website
Clicking the ad leads to a polished website. It may include:
- Before-and-after photos
- Celebrity endorsements (often fake)
- Limited-time countdown timers
- Five-star reviews
A typical herbciepscam site appears legitimate at first glance. However, closer inspection often reveals vague company information and missing legal disclosures.
Step 3: Free Trial or Discount Offer
Consumers are encouraged to try the product at a discounted rate or “free trial.” The catch is hidden in fine print. Many victims later discover they have been enrolled in automatic subscription billing.
Charges may appear monthly, and cancellation procedures can be difficult or impossible.
Step 4: Delivery Issues or Low-Quality Products
Some customers report receiving products that look different from what was advertised. Others never receive anything at all.
In more concerning cases, ingredient lists are incomplete or misleading, posing potential health risks.
Step 5: Data and Payment Risks
Beyond financial loss, herbciepscam operations may compromise personal data. Payment details, email addresses, and phone numbers can be exposed or misused.
This multi-layered risk is what makes such scams particularly harmful.
Key Warning Signs of Herbciepscam
Recognizing red flags early can prevent serious problems. Below are common indicators associated with herbciepscam-type schemes.
Unrealistic Health Claims
If a product claims to cure serious diseases within days or promises guaranteed results without lifestyle changes, skepticism is warranted.
Health improvements rarely happen instantly.
Lack of Company Transparency
Legitimate businesses provide:
- A physical address
- Customer service contact information
- Clear refund policies
- Detailed ingredient lists
When this information is missing or difficult to verify, caution is essential.
High-Pressure Sales Tactics
Countdown clocks, “only 3 bottles left” warnings, and dramatic language are designed to rush decisions. Ethical companies rarely rely on pressure to make sales.
Suspicious Payment Methods
Requests for cryptocurrency, wire transfers, or prepaid cards are major red flags. Secure, traceable payment methods are standard for reputable retailers.
Poor Online Reputation
If you search and find consistent complaints about unauthorized charges, missing deliveries, or non-responsive customer support, it may indicate a herbciepscam pattern.
Real World Examples of Herbciepscam
Although herbciepscam is not a single documented company, real consumer experiences reflect similar scam structures.
One common case involves a “detox herbal supplement” marketed as a breakthrough formula. The website displayed glowing testimonials and medical imagery. After signing up for a discounted trial, the customer noticed recurring charges exceeding the advertised price.
Another example involves a weight-loss capsule claiming to burn fat without diet or exercise. Buyers reported receiving generic packaging with no manufacturer information. Attempts to request refunds went unanswered.
In both scenarios, the marketing tactics and billing methods align with herbciepscam warning signs.
These cases highlight the importance of researching thoroughly before entering payment details.
Risks and Consequences of Herbciepscam
The impact of falling victim to herbciepscam can extend beyond financial loss.
Financial Damage
Unauthorized subscription charges may accumulate over months. Some victims only realize the issue after significant amounts have been withdrawn.
Health Risks
Unregulated herbal products can contain unknown ingredients. Without proper testing, these substances may cause allergic reactions or interact negatively with medications.
Emotional Stress
Being scammed often creates embarrassment and distrust. Victims may feel hesitant to try legitimate wellness products afterward.
Data Exposure
Compromised payment information increases the risk of identity theft or additional fraudulent transactions.
Understanding these risks reinforces the importance of careful evaluation before purchasing health products online.
How to Protect Yourself from Herbciepscam
Taking proactive steps can dramatically reduce your risk.
1. Research the Company
Search for independent reviews and check whether the company has verifiable contact information. Look beyond testimonials displayed on the product’s own website.
2. Examine the Claims
If the marketing sounds too good to be true, it probably is. Real health improvements require evidence and realistic timelines.
3. Read Terms and Conditions
Subscription traps often hide in fine print. Carefully review cancellation policies before completing any purchase.
4. Use Secure Payment Methods
Credit cards typically offer better fraud protection than debit cards or direct transfers.
5. Consult Healthcare Professionals
Before trying new supplements, especially if you have medical conditions, speak with a qualified health professional.
6. Monitor Bank Statements
Regularly reviewing transactions helps you catch unauthorized charges early.
These steps are simple but highly effective in preventing herbciepscam-related losses.
FAQs About Herbciepscam
Is herbciepscam a legitimate brand?
No. The term is generally associated with suspected fraudulent herbal product promotions rather than a verified company.
Are all herbal supplements scams?
Absolutely not. Many reputable companies sell safe, tested herbal products. The issue lies with deceptive marketing and hidden billing practices.
How can I check if a supplement is safe?
Look for transparent ingredient lists, third-party testing certifications, and professional medical guidance. Avoid products with exaggerated promises.
What should I do if I’ve already been charged?
Contact your bank immediately. Request a chargeback if possible and monitor your account for additional suspicious activity.
Why do people keep searching for herbciepscam?
Search interest grows when consumers encounter questionable websites or unexpected billing related to herbal products. The term has become a shorthand warning label for these experiences.
Final Thoughts
Herbciepscam represents a broader problem in the digital marketplace: the misuse of wellness marketing to exploit consumer trust. While natural remedies can be beneficial when responsibly produced and properly tested, fraudulent operators damage the credibility of the entire industry.
The most powerful defense is awareness. By recognizing red flags, verifying claims, and taking your time before making purchases, you significantly reduce your risk.
When it comes to health and money, caution is not paranoia. It is smart decision-making.
-

 Celebrity6 months ago
Celebrity6 months ago3 Facts About Pitbull Singer That Define His Global Fame
-

 Fashion6 months ago
Fashion6 months agoAvant Garde Fashion: Meaning, Impact and Influence
-

 Celebrity6 months ago
Celebrity6 months agoRemembering Paul Dorries: Life, Legacy & Influence
-

 Celebrity6 months ago
Celebrity6 months agoNick Sandmann Net Worth Explained in 2025
-

 Tech5 months ago
Tech5 months agoInflatom: Smart Expansion Technology Redefining Modern Systems
-

 Celebrity6 months ago
Celebrity6 months agoThe Emerging Influence of Nikki Hakuta
-
 Celebrity6 months ago
Celebrity6 months agoWilliam Carlyle Hall: A Comprehensive Guide to His Legacy
-

 Celebrity5 months ago
Celebrity5 months agoHow Much Does Sabrina Carpenter Weigh































