Tech
Pertadad in Tech: Definition, Applications, and Industry Impact
The technology landscape evolves rapidly, introducing new frameworks, concepts, and methodologies that redefine how digital systems operate. One emerging concept gaining attention in tech-focused discussions is Pertadad.
If you’ve encountered this keyword in relation to software development, digital systems, innovation strategy, or IT infrastructure, you’re likely looking for a clear explanation grounded in technology — not internet slang.
This comprehensive guide explores Pertadad from a tech perspective: its definition, benefits, challenges, practical use cases, and how it may influence future innovation models in 2026 and beyond.
What Is Pertadad in Technology?
In the technology context, Pertadad refers to a conceptual framework centered on adaptability, modular architecture, and intelligent digital coordination. It represents a structured yet flexible approach to designing and managing modern systems.
Unlike rigid development models, this framework emphasizes:
- Scalable digital architecture
- Adaptive workflows
- Data-driven decision support
- Continuous system optimization
In simple terms, it describes a mindset and structural model for building resilient, future-ready digital environments.
Why This Framework Is Relevant in 2026 Tech Trends
Several industry shifts make Pertadad especially relevant today:
- Cloud-native infrastructure adoption
- AI-powered automation integration
- Increased demand for scalable microservices
- Cybersecurity-first architecture planning
- Continuous deployment environments
Modern organizations require systems that evolve without complete restructuring. This model supports that need by promoting modularity and strategic flexibility.
Core Principles of Pertadad in Digital Systems
To understand its technical value, we must break down the foundational principles that define Pertadad in tech ecosystems.
1. Modular Architecture
Systems are built as independent components that can scale or update without affecting the entire structure.
2. Adaptive Logic Layers
Business logic adapts based on real-time data inputs, allowing dynamic responses to changing conditions.
3. Integrated Automation
Automation isn’t added later — it’s embedded from the beginning of system design.
4. Continuous Optimization
Performance monitoring tools constantly evaluate and improve system efficiency.
Together, these principles create a robust digital foundation capable of long-term sustainability.
Benefits of Implementing This Approach
Organizations adopting Pertadad-based strategies often experience measurable advantages.
Improved Scalability
Modular design enables businesses to scale services independently without costly reengineering.
Faster Deployment Cycles
Because components are decoupled, development teams can push updates more efficiently.
Enhanced System Resilience
Failure in one module does not collapse the entire infrastructure.
Better Resource Allocation
Automated monitoring reduces manual oversight and improves efficiency.
Challenges of Implementation
Despite its advantages, adopting Pertadad within a technology ecosystem presents challenges.
Initial Complexity
Designing modular, adaptive systems requires advanced planning and skilled engineering teams.
Higher Early Investment
Infrastructure restructuring and training may increase short-term costs.
Integration with Legacy Systems
Older architectures may not support modular or adaptive frameworks easily.
Understanding these limitations helps organizations prepare strategically before transitioning.
Real-World Applications in Modern Technology
To illustrate how Pertadad functions in practice, here are key industry examples.
Cloud Infrastructure Management
Enterprises managing hybrid or multi-cloud environments benefit from modular resource control and automated load balancing.
SaaS Product Development
Software-as-a-Service platforms can use this architectural model to update features without interrupting users.
AI-Driven Systems
Machine learning platforms require adaptive data processing layers, aligning well with continuous optimization principles.
Cybersecurity Architecture
Zero-trust frameworks integrate smoothly within modular security systems built using Pertadad principles.
Step-by-Step Guide to Applying This Model in Your Tech Stack
If your organization wants to implement Pertadad, follow this structured approach:
Step 1: Audit Existing Infrastructure
Identify rigid dependencies and monolithic structures that limit scalability.
Step 2: Design Modular Components
Break applications into independent services or microservices.
Step 3: Integrate Real-Time Monitoring Tools
Use performance dashboards to gather actionable system insights.
Step 4: Implement Automation Layers
Embed automated workflows for testing, deployment, and scaling.
Step 5: Continuously Optimize
Review analytics and refine system architecture regularly.
This gradual transition ensures stability while moving toward a more adaptive model.
Comparison with Traditional System Architecture
Traditional architectures often rely on centralized control and tightly coupled systems. While effective in earlier development eras, they struggle with rapid innovation demands.
Pertadad differs by prioritizing:
- Decentralization
- Data responsiveness
- Incremental scaling
- Automation-first thinking
The result is an infrastructure capable of evolving without complete redesign.
Industry Outlook: The Future of Pertadad
Looking ahead, Pertadad aligns with several future-facing tech movements:
- Edge computing expansion
- AI orchestration platforms
- Autonomous infrastructure management
- Green computing optimization
- Quantum-ready modular frameworks
As enterprises push toward intelligent automation and real-time adaptability, these principles may become increasingly standardized within advanced system design.
Frequently Asked Questions
What does Pertadad mean in tech?
In technology, Pertadad refers to a modular, adaptive system framework designed for scalability, automation, and continuous optimization.
Is Pertadad a programming language?
No. It is not a language but a conceptual architectural approach for building flexible digital ecosystems.
Can startups use Pertadad?
Yes. Startups benefit from scalable design that supports rapid growth without rebuilding infrastructure.
Does Pertadad replace microservices?
Not exactly. It often incorporates microservices but extends beyond them by integrating adaptive intelligence and automation layers.
Is Pertadad suitable for enterprise systems?
Yes. Large enterprises particularly benefit from resilience and scalability in complex environments.
Final Thoughts
In a world where digital transformation accelerates every year, rigid systems struggle to survive. Pertadad offers a structured yet flexible approach to designing future-ready infrastructures.
By focusing on modular architecture, adaptive logic, and automation integration, organizations can build technology stacks that grow, evolve, and respond intelligently to change.
As innovation continues shaping the global tech landscape, Pertadad represents a strategic shift toward sustainable, scalable digital ecosystems built for the demands of 2026 and beyond.
Blog
534534r3 Explained Trends, Uses and Insights

In today’s fast-changing digital environment, unusual keywords and coded terms continue to appear and spark curiosity. Among these, 534534r3 stands out because it looks random yet often carries a specific purpose. As a result, many users feel confused when they encounter it in systems, platforms, or technical environments.
So, why does this term matter? More importantly, how should you interpret it? In this guide, you will gain a clear understanding of 534534r3, including its meaning, uses, benefits, and practical applications. Along the way, you will also see how such identifiers play a role in modern digital systems.
What is 534534r3
At its core, 534534r3 functions as an alphanumeric identifier. In other words, it combines numbers and letters to create a unique reference. Although it does not represent a widely known concept, it still follows a common pattern used across many systems.
More specifically, developers and platforms use similar structures to manage data efficiently. Therefore, instead of focusing on a fixed definition, you should look at how and where the term appears.
Key Interpretations
- It can act as a system-generated identifier for unique records
- It may serve as a placeholder during testing or development
- It can represent a coded reference linked to internal data
Because of this flexibility, the meaning of 534534r3 always depends on its context.
Understanding User Intent and Context
When users search for 534534r3, they usually want clarity. In many cases, they have already seen the term somewhere and now need a simple explanation. Therefore, understanding intent becomes essential.
Related Concepts
- Alphanumeric identifiers in software systems
- Placeholder values in development environments
- Data organization and indexing methods
- Tracking codes used in digital platforms
Why People Search This Keyword
First, some users encounter the term and want to know what it means. Next, others work with systems and need technical clarity. Finally, a group of users explores how unique identifiers function in general.
As a result, addressing all these perspectives ensures a complete and useful explanation.
Benefits of Using Structured Identifiers Like 534534r3
Structured identifiers such as 534534r3 offer several clear advantages. When used correctly, they improve how systems handle and organize data.
Better Organization
First of all, unique identifiers allow systems to arrange large amounts of data efficiently. Since each item has its own code, duplication becomes much less likely.
Accurate Tracking
In addition, these identifiers help track actions, records, and processes. Because each code is unique, systems can follow activities without confusion.
Scalability
As systems grow, organization becomes more complex. However, structured identifiers maintain order, which allows platforms to expand without losing efficiency.
Controlled Testing
At the same time, developers use identifiers like 534534r3 during testing. This approach allows them to simulate real scenarios without affecting actual data.
Challenges and Limitations
Despite these advantages, 534534r3 also presents certain challenges. Therefore, understanding its limitations helps avoid potential issues.
Limited Understanding
To begin with, most users do not recognize the meaning of such identifiers. Consequently, confusion may arise.
Context Dependence
Furthermore, the value of the keyword depends entirely on its usage. Without context, it becomes difficult to interpret.
Low Visibility
Since it is not widely known, it does not naturally attract attention. As a result, it requires explanation to become useful.
Risk of Misinterpretation
Finally, if you do not label it properly, users may misunderstand its purpose. This can lead to errors or inefficiencies.
Real World Applications
Although 534534r3 itself may seem abstract, similar identifiers appear in many real situations. In fact, they play a crucial role in various industries.
Database Systems
For example, databases assign unique codes to each record. This system ensures that every entry remains distinct and easy to locate.
E commerce Platforms
Similarly, online stores use unique identifiers to manage products. These codes help track inventory, process orders, and maintain accuracy.
Software Development
During development, teams rely on placeholder values. In this case, identifiers like 534534r3 allow systems to function before real data becomes available.
Digital Tracking
Moreover, platforms use unique codes to monitor user actions and system performance. This approach improves analysis and decision-making.
How to Use 534534r3 Effectively
If you plan to use 534534r3, you should follow a structured process. By doing so, you ensure clarity and efficiency.
Step by Step Process
- First, define the purpose of the identifier clearly
- Next, maintain a consistent format across systems
- Then, add context or labels for better understanding
- Finally, monitor performance and adjust when necessary
By following these steps, you reduce confusion and improve usability.
Tools and Best Practices
To manage identifiers effectively, you need both the right tools and a clear strategy.
Useful Tools
- Data management platforms to organize structured information
- Analytics tools to track usage and performance
- Monitoring tools to observe system behavior
Best Practices
- Always pair identifiers with clear descriptions
- Avoid using random codes without explanation
- Keep formats simple and consistent
- Regularly review and update identifiers
As a result, these practices help maintain clarity and long-term efficiency.
Frequently Asked Questions
What does 534534r3 mean
It represents an alphanumeric identifier used for tracking, categorizing, or testing within a system.
Is 534534r3 a real keyword
Yes, although it appears in niche or technical contexts rather than general usage.
Why would someone use 534534r3
They use it to manage data, test systems, or organize information more effectively.
Can 534534r3 be important
Yes, especially in technical systems where unique identifiers play a critical role.
Is 534534r3 useful for general users
In most cases, it becomes relevant only when users interact with systems that rely on such identifiers.
Conclusion
In summary, 534534r3 may look like a random string, yet it represents a powerful concept in digital systems. Throughout this guide, you have seen how structured identifiers improve organization, tracking, and scalability.
Moreover, understanding these identifiers helps you navigate modern systems with greater confidence. As digital environments continue to evolve, such structures will remain essential for managing complex data efficiently.
Tech
Surge Protection and Electrical Safety for Ductless Mini-Split Longevity: The Overlooked Factor Behind System Failure
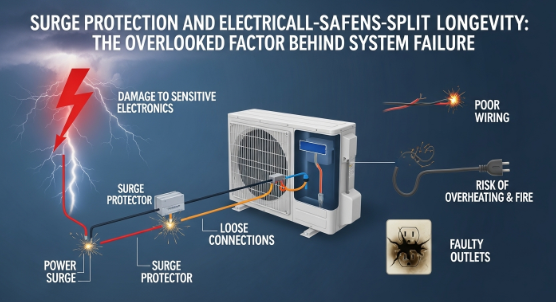
A ductless mini-split system is known for being quiet, energy-efficient, and reliable. Many homeowners choose it because it cools and heats rooms without bulky ductwork. It also helps lower energy bills when compared to older HVAC systems.
But even a high-quality mini-split can fail early if the electrical system is not safe or stable. In fact, many costly breakdowns do not start inside the HVAC unit. They start in the home’s wiring or power supply. Small electrical issues can slowly damage sensitive parts until the system stops working.
Understanding electrical safety is important if you want your system to last for years. This includes surge protection, proper installation, and regular inspection. Without these, even a brand-new system may need early ductless mini split repair houston services.
Why Mini-Splits Are So Sensitive to Electrical Issues
Modern mini-splits are different from older HVAC systems. They use inverter technology and advanced control boards. These parts help the system run at variable speeds and save energy.
However, these same components are also very sensitive. They depend on steady voltage and clean electrical flow. Even small changes in power can create stress inside the system.
Key parts that are vulnerable include:
- Inverter boards
- Outdoor condenser control units
- Communication wiring between indoor and outdoor units
- Power supply modules
If voltage rises or drops quickly, it can damage these components. Sometimes the damage is immediate. Other times, it builds slowly over time and leads to sudden failure later.
Hidden Electrical Problems Most Homeowners Miss
Electrical issues are not always easy to notice. Many homes have small problems that go undetected for years. These issues can slowly affect HVAC performance without clear warning signs.
Some common hidden problems include:
- Small power surges when large appliances turn on
- Loose or aging neutral wires
- Outdated electrical panels in older homes
- Circuits that are overloaded after new installations
- Poor grounding in the electrical system
- Voltage changes caused by neighborhood demand
At first, these problems may not seem serious. Lights may still work fine, and other appliances may run normally. But a mini-split system reacts differently because it is more sensitive.
Over time, these small issues can lead to strange system behavior. Homeowners may think the HVAC system is failing when the real issue is electrical.
In many cases, proper inspection by professionals who offer electrical services houston tx can uncover the real cause before major damage happens.
When HVAC Problems Are Really Electrical Problems
Many mini-split issues are misdiagnosed. A homeowner may see error codes or performance problems and assume the system is broken. But the real cause is often unstable power.
Here are some common symptoms that may point to electrical trouble:
- The system shuts off randomly
- The unit restarts on its own
- Cooling or heating feels weak
- Breaker trips without warning
- Error codes appear and disappear
- Outdoor unit does not start consistently
These signs do not always mean the HVAC system is damaged. Instead, they may indicate power fluctuations or wiring issues.
This is why HVAC technicians and electricians often need to work together. A system may be repaired multiple times when the real issue is electrical. That is why homeowners sometimes end up needing ductless mini split repair houston services more than expected.
A full electrical check can save time, money, and stress.
Surge Protection: A Small Device That Prevents Big Repairs
One of the easiest ways to protect a mini-split system is surge protection. A surge happens when there is a sudden spike in electrical voltage. This can be caused by storms, grid switching, or large appliances turning on and off.
Surge protectors help absorb or redirect this extra voltage so it does not reach your HVAC system.
There are a few types of protection:
- Whole-Home Surge Protection: This is installed at the main electrical panel. It protects the entire home from large power spikes.
- Dedicated HVAC Surge Protection: This type protects only the mini-split system. It adds another layer of safety for sensitive equipment.
- Point-of-Use Protection: This is installed near the unit itself for added defense.
Surge protection works like a shield. It does not stop electricity from flowing, but it controls dangerous spikes before they can cause harm.
This small investment can help avoid expensive repairs and reduce the need for frequent ductless mini split repair houston service calls.
Why Proper Electrical Installation Matters
Even the best mini-split system will not perform well if the electrical setup is poor. Proper installation is just as important as the equipment itself.
A safe installation should include:
- A dedicated circuit for the mini-split
- Correct breaker size for the system load
- Proper grounding and bonding
- Clean and secure wiring connections
- Compliance with local electrical codes
If any of these steps are skipped, the system may struggle from the start. It may also wear out faster or break down more often.
Poor installation is one of the top reasons homeowners need early repairs. In some cases, repeated service calls for electrical services houston tx are needed to fix issues that should have been handled during installation.
Good electrical work helps the system run smoothly, use less energy, and last longer.
Why Electrical Safety Matters More Today Than Ever
Homes today use more electricity than in the past. Many households now have smart devices, large appliances, EV chargers, and entertainment systems running at the same time.
This higher demand puts more stress on electrical systems. It increases the chance of voltage drops and small surges throughout the day.
Weather also plays a role. Storms and power grid fluctuations can cause sudden spikes in electricity. These events are becoming more common in many areas.
Because of this, surge protection and electrical safety are no longer optional. They are necessary for protecting expensive systems like ductless mini-splits.
Without protection, homeowners may face repeated breakdowns and higher repair costs over time.
Simple Ways to Protect Your Mini-Split System
Homeowners can take a few simple steps to reduce electrical risks:
- Schedule regular electrical inspections
- Install surge protection devices
- Avoid overloading circuits
- Keep outdoor units clear and dry
- Check for flickering lights or breaker issues
- Use licensed professionals for repairs and upgrades
These small actions can make a big difference in system performance.
Working with experts who provide electrical services houston tx can help ensure your home is safe and up to date.
Final Thoughts
A ductless mini-split system is a smart investment for comfort and energy savings. But its long-term performance depends on more than just HVAC maintenance. Electrical safety plays a major role in how well the system works over time.
Surge protection, proper installation, and stable wiring all help protect sensitive components inside the system. Without these protections, even small electrical problems can lead to major breakdowns.
If your system is acting strangely or you want to prevent future issues, it is important to get professional help early. Many problems that seem like HVAC failures are actually electrical in nature.
For dependable ductless mini split repair houston homeowners can trust, and expert electrical services houston tx, Valderrama A/C & Refrigerator provides support to keep systems safe, efficient, and reliable year-round.
Tech
Moving from On-Premises to Cloud Databases: A Modernization Roadmap

Databases are the backbone of modern enterprises, powering everything from transactional systems to advanced analytics. Yet many organizations still rely on on-premises databases that struggle to keep up with the demands of today’s digital economy. These systems often present challenges, including limited scalability, high maintenance costs, and restricted access to real-time insights.
That’s why more businesses are turning to cloud databases as part of their digital transformation journey. To make this shift seamless, organizations are leveraging expert database modernization services—solutions that provide the expertise, tools, and methodologies to efficiently and securely migrate legacy systems to the cloud.
In this blog, we’ll outline the roadmap for migrating from on-premises to cloud databases, highlight common pitfalls, and explain how modernization services can accelerate success.
Why Move to Cloud Databases?
Shifting from on-premises databases to the cloud is not just a technology upgrade—it’s a strategic move that aligns IT with long-term business goals. Key drivers include:
- Scalability: Cloud databases enable organizations to scale up or down instantly in response to workload demands.
- Cost efficiency: Eliminating hardware and maintenance costs reduces the total cost of ownership.
- Agility and innovation: Cloud platforms integrate with AI, analytics, and automation tools to deliver real-time insights.
- Global accessibility: Teams can securely access data from anywhere, supporting remote and distributed workforces.
- Enhanced security: Leading cloud providers invest heavily in compliance and advanced security features.
By embracing database modernization services, organizations ensure that these benefits are realized quickly and with minimal disruption.
The Roadmap to Database Modernization
A successful transition to cloud databases requires a structured approach. You can fast-track your data modernization journey with Microsoft Services. Below is a step-by-step roadmap supported by database modernization services.
1. Assess the Current Landscape
The first step is understanding your existing database environment:
- What types of databases are in use (SQL, Oracle, MySQL, etc.)?
- Which applications and business processes depend on them?
- Are there performance or compliance issues?
How Services Help:
Specialized database modernization services perform detailed assessments to map dependencies, identify risks, and prioritize databases for migration.
2. Define Business Objectives
Modernization is not just an IT project—it’s about aligning technology with business goals. Objectives may include:
- Reducing costs.
- Enabling real-time analytics.
- Improving compliance.
- Supporting global expansion.
How Services Help:
Consultants ensure that modernization goals tie directly to measurable business outcomes, ensuring stakeholder buy-in.
3. Choose the Right Cloud Strategy
Not all migrations are the same. Common approaches include:
- Rehosting (“Lift and Shift”): Moving databases as-is to the cloud.
- Refactoring: Optimizing schemas and code for cloud-native performance.
- Replatforming: Adapting databases to run more efficiently in cloud environments.
How Services Help:
With database modernization services, experts guide organizations in selecting the most cost-effective and scalable strategy for each workload.
4. Plan Data Migration
Data migration is one of the most complex steps. Challenges include data cleansing, deduplication, and ensuring minimal downtime.
How Services Help:
Consultants use advanced tools and proven methodologies to migrate data securely, while ensuring accuracy, consistency, and business continuity.
5. Implement Security and Compliance Controls
Data is one of the most valuable assets, making security a top priority. Organizations must address encryption, access controls, and compliance with regulations like GDPR, HIPAA, or CCPA.
How Services Help:
Expert database modernization services ensure cloud databases meet stringent security standards and industry regulations, reducing compliance risks.
6. Optimize Performance
After migration, optimization ensures cloud databases deliver maximum value. This includes fine-tuning queries, adjusting configurations, and integrating analytics tools.
How Services Help:
Consultants monitor workloads post-migration and continuously optimize performance for speed, efficiency, and scalability.
7. Enable Continuous Monitoring and Support
Modernization doesn’t end once the database is in the cloud. Ongoing monitoring and support are crucial to detect issues early, maintain compliance, and prepare for future upgrades.
How Services Help:
With proactive monitoring, database modernization services ensure stability, scalability, and long-term ROI.
Common Pitfalls in Database Modernization
Even with a roadmap, organizations often face pitfalls such as:
- Underestimating complexity: Legacy databases may contain decades of poorly documented customizations.
- Ignoring data quality issues: Migrating dirty or redundant data creates problems in the new system.
- Inadequate testing: Skipping validation can lead to inaccurate data or system outages post-migration.
- Lack of stakeholder involvement: Modernization efforts may fail if business users aren’t engaged.
Engaging database modernization services helps organizations sidestep these issues with tested frameworks and expert guidance.
Best Practices for Successful Modernization
To maximize success, organizations should follow these best practices:
- Start with a pilot project: Migrate a non-critical workload first to validate processes.
- Prioritize data quality: Cleanse and standardize data before migration.
- Engage stakeholders: Align technical execution with business requirements.
- Adopt automation: Use migration tools to reduce manual errors.
- Plan for training: Equip teams with skills to manage cloud environments.
- Monitor continuously: Proactive monitoring ensures long-term reliability.
With the guidance of skilled database modernization services, these practices become part of a structured, risk-free journey.
The Strategic Value of Database Modernization Services
Beyond the technical migration, database modernization services provide strategic value:
- Faster innovation: Cloud-native databases integrate seamlessly with AI, ML, and analytics.
- Future-readiness: Modern databases adapt to evolving business needs and digital strategies.
- Improved agility: Organizations respond faster to market changes and customer demands.
- Stronger compliance: Built-in security features reduce the risk of breaches and penalties.
This ensures modernization is not just a one-time project but a long-term competitive advantage.
Final Thoughts
Moving from on-premises to cloud databases is no longer optional—it’s a necessity for organizations aiming to stay competitive in the digital era. But the journey is complex, and mistakes can be costly.
That’s why businesses are increasingly relying on expert database modernization services. With structured roadmaps, proven methodologies, and ongoing support, these services ensure migrations are smooth, secure, and strategically aligned.
The future of data is in the cloud—and with the right modernization roadmap, businesses can unlock agility, innovation, and growth like never before.
-

 Celebrity4 months ago
Celebrity4 months ago3 Facts About Pitbull Singer That Define His Global Fame
-

 Fashion4 months ago
Fashion4 months agoAvant Garde Fashion: Meaning, Impact and Influence
-

 Celebrity4 months ago
Celebrity4 months agoRemembering Paul Dorries: Life, Legacy & Influence
-

 Tech4 months ago
Tech4 months agoInflatom: Smart Expansion Technology Redefining Modern Systems
-

 Celebrity4 months ago
Celebrity4 months agoNick Sandmann Net Worth Explained in 2025
-

 Celebrity4 months ago
Celebrity4 months agoThe Emerging Influence of Nikki Hakuta
-

 Entertainment4 months ago
Entertainment4 months agoFun Craft Thunderonthegulf Creative Adventures
-

 Entertainment4 months ago
Entertainment4 months agoDetroit Lions vs 49ers Match Player Stats: Full Breakdown & Analysis
































